Cloudflare AI agents can now buy domains and deploy apps, and I had to read the announcement twice because this is exactly where the agent story stops being cute.
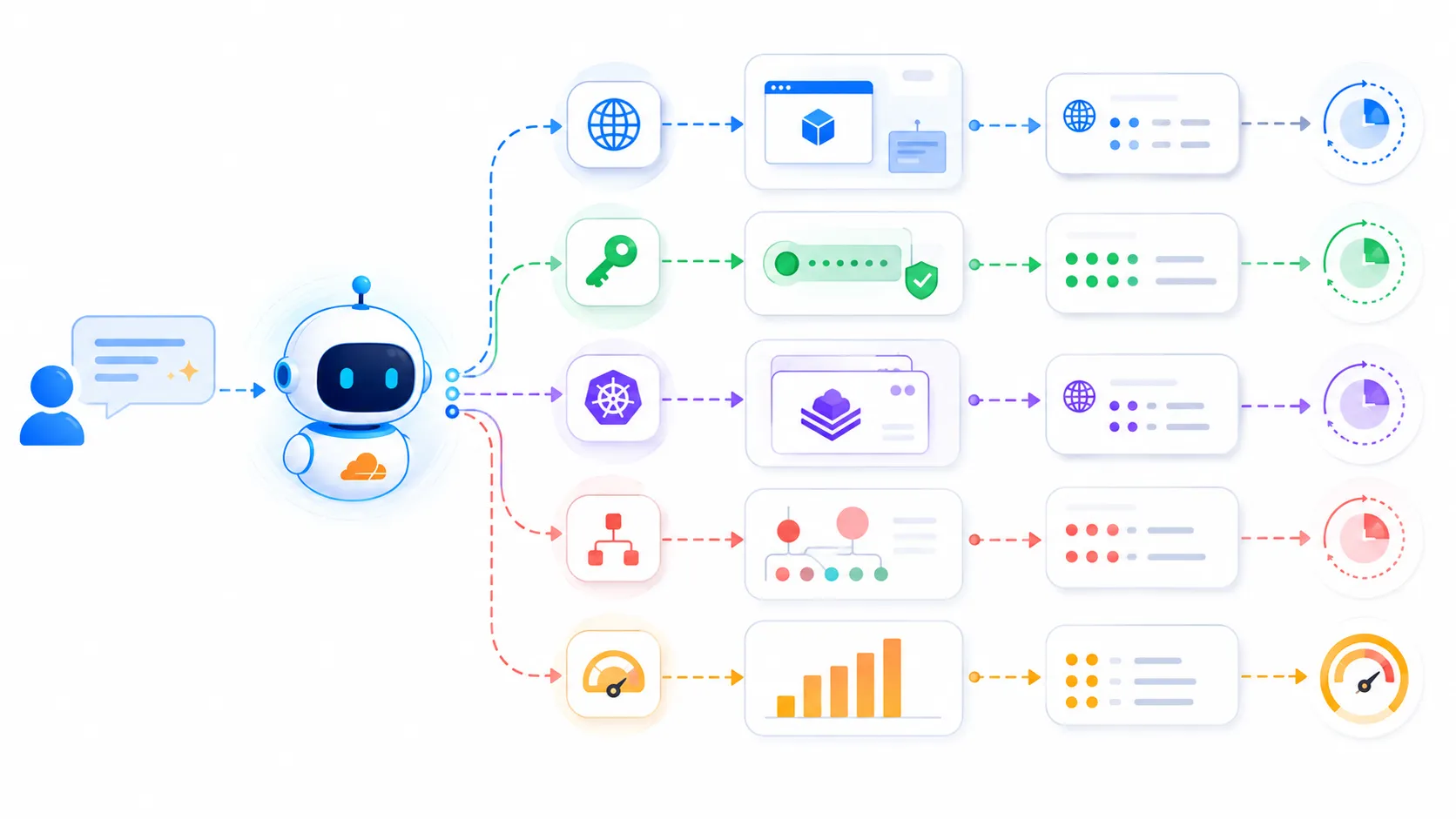
Not “generate a landing page.” Not “open a pull request.” The new loop is closer to: create the cloud account, start the paid subscription, register the domain, fetch the API token, and put the app in production. That is a very different class of permission.
The Cloudflare announcement says the flow is built with Stripe Projects. The human still accepts Cloudflare’s terms, and approvals can happen when needed, but the boring dashboard work is no longer assumed to be human work. Stripe’s own Sessions 2026 post frames the same thing more bluntly: developers or agents can sign up for, purchase, and integrate the services needed to deploy products from wherever they write or prompt code.
Honestly? This is both obviously useful and obviously uncomfortable.
If you have spent any time shipping tiny tools, prototypes, customer-specific demos, or internal dashboards, you already know the pain Cloudflare is attacking. The agent can write code for twenty minutes, then everything falls apart because it needs a domain, a token, a storage bucket, a billing plan, or a provider account. So the human returns to browser-tabs-as-devops, copies credentials, pastes them into .env, and then pretends the context switch was no big deal.

That gap was always weird. We let agents edit code, but then forced them to stop at the exact moment the software needs to touch reality.
Cloudflare AI Agents Buy Domains Because Provisioning Was The Wall
The boring part became the product surface
The actual mechanics are not magic. Stripe Projects exposes a CLI workflow where a project can add providers, provision services, sync credentials, and manage billing from one command-line surface. Cloudflare plugs into that as a provider. In the Cloudflare demo path, the agent discovers available services, gets authorization through the signed-in Stripe user, receives credentials, and uses a payment token instead of raw card details.
That last detail matters. The agent is not supposed to see your credit card number. Cloudflare says Stripe includes a payment token in the provider request, and there is a default spend limit of 100 USD per month per provider. That is not the same thing as “safe,” but it is a lot better than handing a general-purpose coding agent a real card and a blank terminal.
Still, I can already hear the production incident review.
Someone will ask, “Why did the agent buy three domains?”
Someone else will say, “It was following the prompt.”
And the room will get quiet because technically both statements are true.
Zero to production is not the same as ready for production
Computerworld’s coverage framed the obvious enterprise worry: once agents can handle provisioning, billing, and deployment, teams inherit new governance and accountability problems. That is the right concern. The scary part is not that an agent can create a Cloudflare account. Humans create messy cloud accounts every day. The scary part is that the action becomes cheap enough to happen repeatedly, automatically, and inside a dev loop where nobody feels like they are “doing infrastructure.”
I had the same reaction after writing about Anthropic still needing engineers while AI coding gets louder. The interesting work keeps moving away from typing code and toward deciding what the system is allowed to do. That sounds abstract until the system is allowed to spend money, register names, issue credentials, and publish reachable endpoints.
Here is the line I would draw:
| Agent action | Default posture |
|---|---|
| Generate code locally | Allow with review |
| Create preview deployment | Allow with quota |
| Register domain | Require explicit approval |
| Start paid plan | Require explicit approval |
| Issue production token | Require scoped approval |
| Change DNS or mail records | Require human confirmation |
That table is not anti-agent. It is pro-sleep.
The Developer Workflow Actually Gets Better
The old setup tax was worse than we admitted
I do not want to pretend this is only a governance story. The developer experience win is real.
Every serious builder has lost time to setup sludge. You start with a simple idea. You need hosting. Then auth. Then a database. Then storage. Then analytics. Then email. Each provider asks you to create an account, pick a plan, verify an email, create a token, copy env vars, read docs, and wire it all together. None of that feels like product work, but it still consumes product time.
Stripe Projects is basically saying: make provisioning part of the same command surface where the code is being written. Cloudflare is saying: if the agent needs infrastructure, let it request infrastructure with a standard protocol instead of sending the user through a signup maze.
That is the right direction.
The best version of this is not “agents secretly run your company.” The best version is a clean permission boundary:
agent_permissions:
preview:
deploy: true
create_subdomain: true
monthly_budget_usd: 20
production:
deploy: require_approval
register_domain: require_approval
create_api_token: scoped_only
change_dns: require_approval
audit:
log_prompt: true
log_cli_command: true
log_provider_response: true
Try running that mental config against your current agent setup. If the answer is “we do not have a place to express those rules,” that is the actual problem. The model is not the boundary. The workflow is.
The New Risk Is Agentic Infrastructure Drift
Your cloud inventory can now grow from prompts
The phrase I keep coming back to is agentic infrastructure drift. We already have regular infrastructure drift: forgotten buckets, stale DNS records, preview apps nobody deleted, service accounts with vague names, old tokens that still work because touching them feels risky.
Now imagine that drift generated by agents.
This is where the Cloudflare and Stripe approach needs to be judged by boring operational details. Can teams query every agent-created resource? Can the billing owner see which prompt caused a purchase? Can a security engineer revoke a token without breaking unrelated work? Can a platform team set organization-wide budgets and provider allowlists? Can a junior developer use the flow without accidentally creating production-shaped resources?
Those questions are not edge cases. They are the product.
If an agent provisions a throwaway database for a prototype, great. If it registers a domain that looks like a real product name, ships a half-reviewed endpoint, and creates a durable token with broad permissions, that is not a prototype anymore. That is a future ticket with a weird audit trail.
The approval UX has to be brutally specific
“Approve deployment” is too vague.
The approval screen needs to say what will be created, what it will cost, who owns it, how long it should live, which credentials will exist, and what the rollback path is. Otherwise we are just recreating the worst parts of OAuth consent screens, except now the app asking for access is an agent that just wrote 1,400 lines of code and is very confident about the next step.
I want approval prompts that look more like a Terraform plan than a chatbot confirmation.
Something like:
Agent wants to:
- create Cloudflare account: personal-workspace-demo
- register domain: example-labs-demo.com
- start plan: pay-as-you-go, capped at 100 USD monthly
- create token: Pages deploy only, expires in 7 days
- deploy project: preview build from commit abc123
Approve for 24 hours?
That would make me much more comfortable than “Looks good?”
What I Would Change Before Letting This Near A Team
Treat agent-created infrastructure as a separate class
If I were rolling this into a team this week, I would not start with production deploys. I would start with preview environments and hard expiration.
Give agents a sandbox namespace. Make every resource tagged with created_by=agent, owner=user, reason=prompt, and expires_at. Set budgets lower than people think they need. Keep domain registration behind a human approval until the team has seen enough logs to trust the flow. Require scoped, short-lived tokens. Make deletion easy.
Then watch what people actually do.
The funny part is that this may make platform engineering more important, not less. Agents can remove setup clicks, but someone still has to design the paved road. Someone has to decide which providers are allowed, which plans are safe, which regions are okay, which names are blocked, which logs matter, and what happens when the agent does exactly what the prompt asked but not what the business wanted.
That is the real story here.
Cloudflare and Stripe are not just making agents more powerful. They are moving the boundary of software creation from code generation into account creation, payment, identity, credentials, DNS, and deployment. That is a huge productivity unlock for solo builders and a huge governance test for teams.
I want this workflow. I also want it behind budgets, audit logs, scoped tokens, approval plans, and resource cleanup that does not rely on someone remembering a demo from last Tuesday.
The agent can ship the app. Fine. But the platform still has to make shipping boring enough that we can trust it.